The New Reality: Why Traditional Supply Chain Security Isn’t Enough
Supply chains have transformed dramatically over the past decade. What once operated as linear, predictable networks have evolved into complex, multi-enterprise supply chain networks spanning continents, technologies, and countless third-party relationships. With this evolution comes unprecedented vulnerability. A single compromised supplier, an unsecured API, or inadequate data governance can cascade into enterprise-wide disruptions. That’s why building cyber-resilient, zero-trust digital networks isn’t just an IT priority—it’s a business imperative.
The good news? Organizations worldwide are recognizing that enterprise supply chain architecture must be reimagined from the ground up with security, governance, and resilience baked in rather than bolted on. Let’s explore how forward-thinking companies are building the supply chain infrastructure of the future.
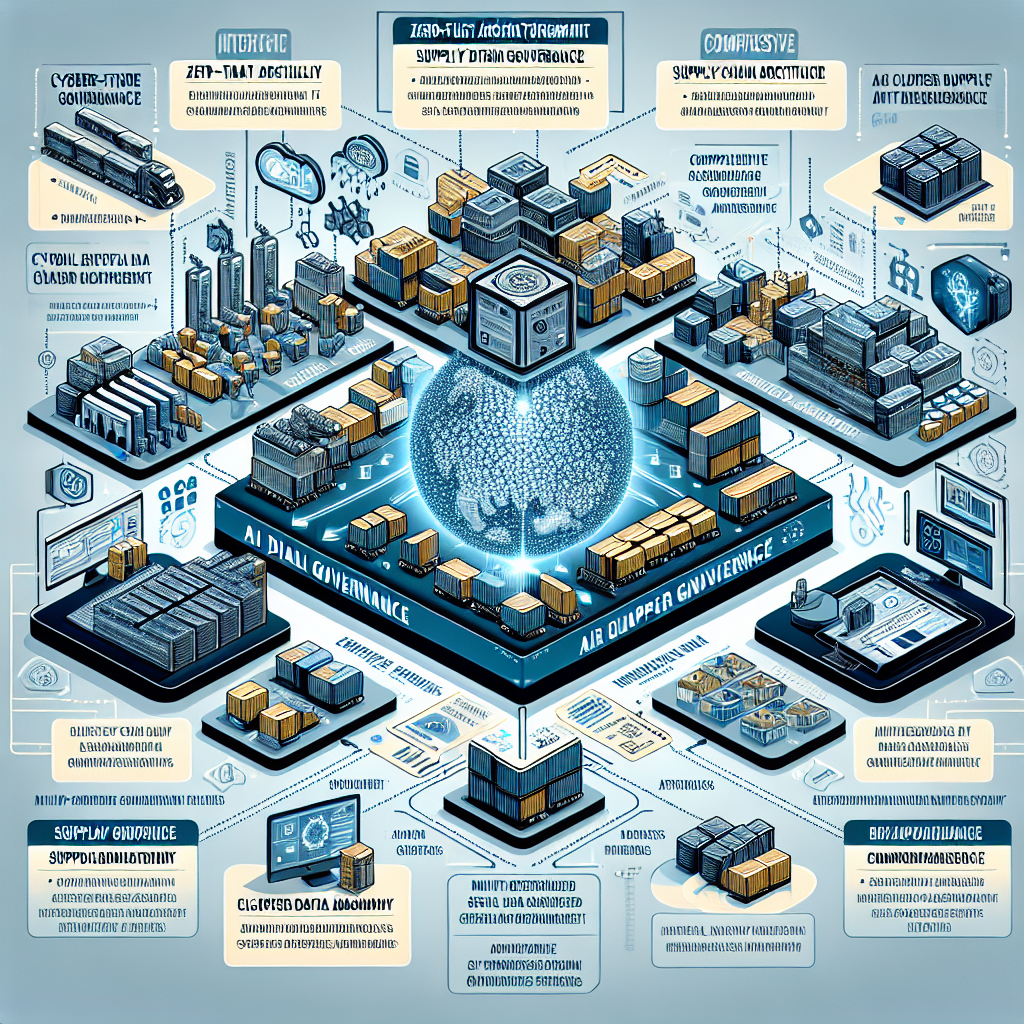
Understanding Zero-Trust Supply Chain Architecture
The zero-trust model operates on a simple principle: never trust, always verify. In the context of supply chains, this means abandoning the outdated assumption that anything inside your network perimeter is safe. Zero-trust supply chain architecture treats every connection, every data exchange, and every access request as potentially compromised until proven otherwise.
This approach is particularly crucial for digital supply chain architecture, where data flows continuously between manufacturers, distributors, logistics providers, and retailers. Implementing zero-trust means establishing strict supply chain identity and access management protocols that authenticate and authorize every interaction, whether it’s a human user, an IoT device, or an automated system.
Key Components of Zero-Trust Implementation
Building a zero-trust framework requires several foundational elements. Micro-segmentation divides your network into secure zones, ensuring that even if one segment is compromised, the breach doesn’t spread. Supply chain IT governance policies must define clear boundaries around who can access what data, when, and under what conditions. Continuous monitoring and verification ensure that access privileges remain appropriate throughout the lifecycle of every relationship and transaction.
Establishing Robust Supply Chain Data Governance
Data is the lifeblood of modern supply chains, but without proper governance, it becomes a liability. Supply chain data governance encompasses the policies, procedures, and standards that ensure data remains accurate, secure, and compliant throughout its lifecycle. This includes everything from supplier data governance to master data management supply chain initiatives that create single sources of truth across disparate systems.
One critical aspect often overlooked is data lineage in supply chain systems. Understanding where data originates, how it’s transformed, who accesses it, and where it ultimately resides is essential for both security and regulatory compliance. When you can trace data’s journey from end to end, you gain both supply chain auditability and the ability to quickly identify and contain breaches or quality issues.
The Role of Data Standardization
Supply chain data standardization might sound tedious, but it’s fundamental to both security and efficiency. When every partner uses different formats, identifiers, and protocols, integration becomes complex and error-prone—creating security gaps. Establishing common standards for product codes, location identifiers, transaction formats, and communication protocols reduces complexity while enhancing interoperability in supply chain systems. This standardization also supports AI governance in supply chain applications by ensuring algorithms receive consistent, high-quality data.
Building Cyber-Resilience in Logistics
Cyber-resilience goes beyond prevention—it’s about maintaining operations even when attacks occur. Cyber-resilience in logistics means designing systems that can detect threats quickly, contain damage effectively, and recover operations rapidly. This requires both technical capabilities and organizational preparedness.
Resilient supply chain architecture design incorporates redundancy at multiple levels: alternative suppliers, backup communication channels, and failover systems that activate automatically when primary systems are compromised. It also means implementing risk governance frameworks in logistics that continuously assess vulnerabilities and prioritize mitigation efforts based on potential business impact.