Modern supply chains are under more pressure than ever — not just to move goods efficiently, but to do so securely, transparently, and in compliance with a growing web of global regulations. As organizations lean into digital transformation, the architecture underpinning their supply chain operations has to be built for resilience, not just speed. Whether you’re a logistics manager, a CIO, or a supply chain architect, understanding how AI governance, zero-trust principles, and data compliance fit together is no longer optional — it’s essential.
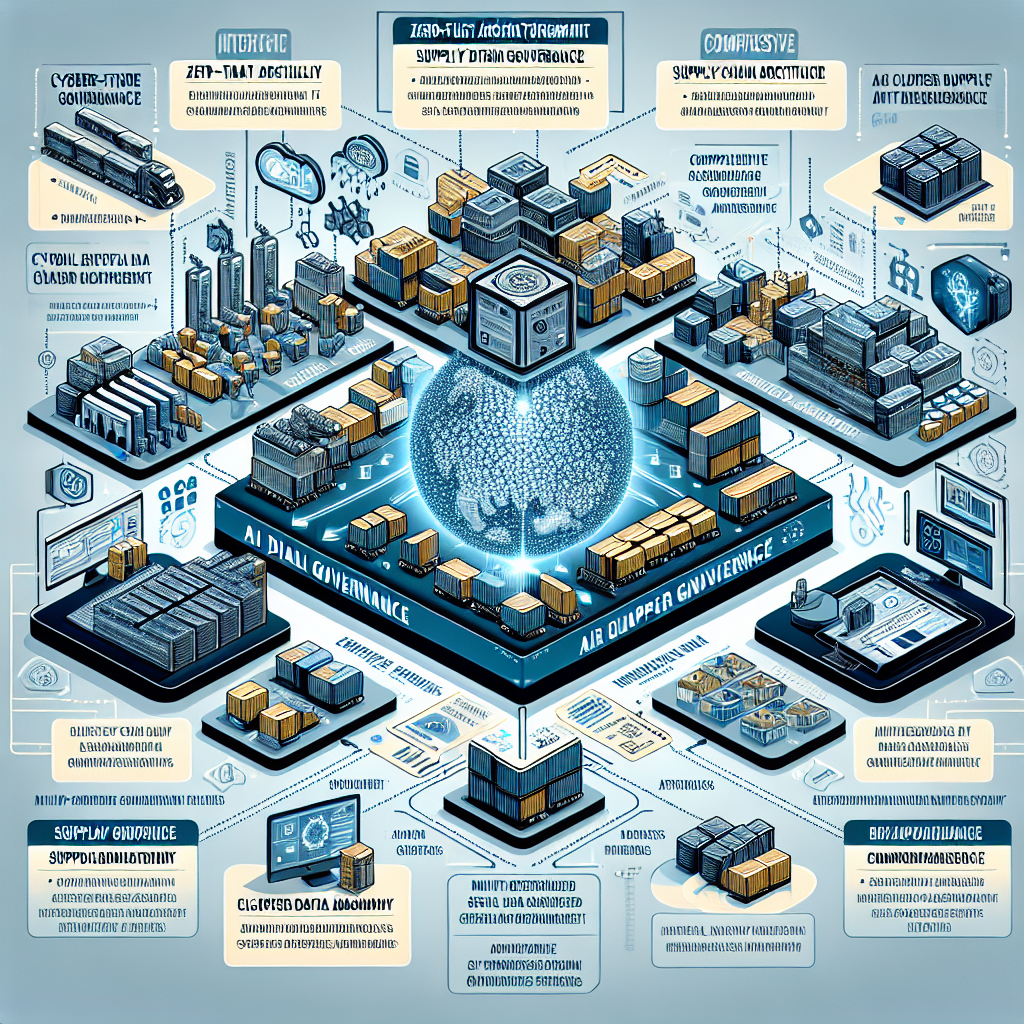
Why AI Governance in Supply Chain Can’t Be an Afterthought
AI is doing a lot of heavy lifting in today’s supply chains — from demand forecasting and route optimization to anomaly detection and supplier risk scoring. But with great automation comes great responsibility. AI governance in supply chain means having clear policies, accountability structures, and audit trails around how AI models are trained, deployed, and monitored.
A concrete example: a global retailer using AI to flag high-risk suppliers needs to ensure that the model’s decisions are explainable, bias-free, and aligned with regulatory expectations — especially in jurisdictions like the EU where the AI Act is reshaping compliance obligations. Without a governance layer, you’re essentially letting an algorithm make high-stakes decisions with no checks in place.
Supply chain IT governance frameworks need to address the full AI lifecycle — not just the shiny deployment phase. That includes version control for models, documentation of training data sources, and ongoing performance monitoring to catch model drift before it causes real-world disruption.
● AI governance requires explainability, accountability, and continuous model monitoring
● Regulatory frameworks like the EU AI Act are directly impacting supply chain AI deployment
● Supply chain IT governance must cover the full AI lifecycle, not just implementation
Zero-Trust Supply Chain Architecture: Trust Nobody, Verify Everything
The Case for Zero-Trust in Multi-Enterprise Environments
Traditional perimeter-based security is simply not built for the realities of modern, multi-enterprise supply chain networks. When you’re sharing data across dozens of suppliers, logistics partners, and cloud platforms, assuming that anything inside your network is “safe” is a dangerous bet. Zero-trust supply chain architecture flips this assumption entirely — every user, device, and service must be authenticated and authorized, every single time.
Consider how a major automotive OEM might manage access across hundreds of Tier 1 and Tier 2 suppliers. With a zero-trust model, even a trusted long-term vendor can’t access sensitive production schedules or engineering data without passing through continuous verification checkpoints. This dramatically reduces the blast radius of a potential breach.
Supply chain identity and access management (IAM) is the backbone of this approach. Role-based access controls, multi-factor authentication, and least-privilege principles ensure that partners only see what they need to see — nothing more. Layered on top of a well-designed digital supply chain architecture, IAM becomes a powerful tool for both security and compliance.
● Zero-trust eliminates implicit trust across complex supplier ecosystems
● Supply chain IAM controls access through role-based and least-privilege principles
● Continuous authentication reduces breach impact in multi-enterprise environments
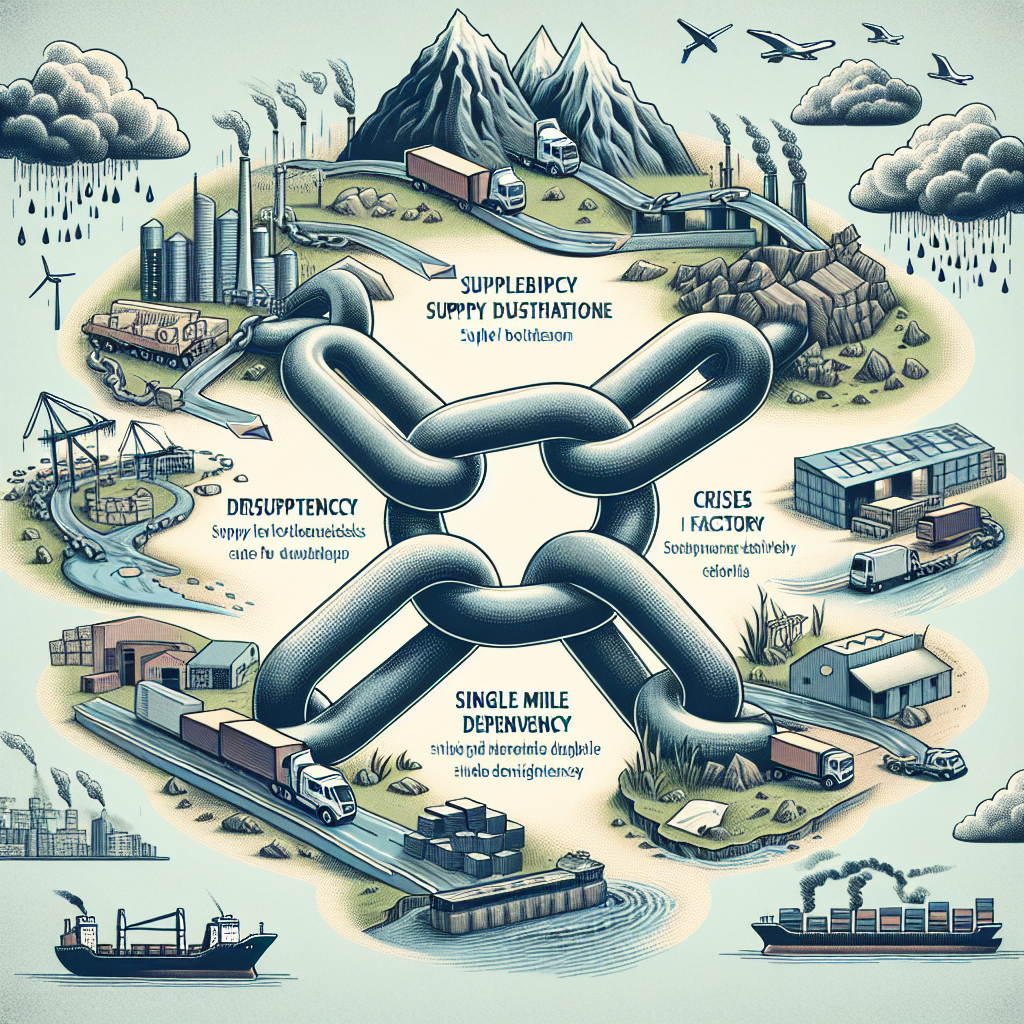
Cyber-Resilience in Logistics: More Than Just Cybersecurity
Cyber-resilience in logistics goes beyond firewalls and antivirus software — it’s about designing systems that can absorb attacks, adapt quickly, and keep operations running even when something goes wrong. The SolarWinds and NotPetya incidents showed the supply chain world just how devastating a cyberattack on a single node can be when systems are tightly coupled with no resilience built in.
Building resilience means investing in redundant systems, real-time threat intelligence sharing, and incident response playbooks that are specific to supply chain scenarios. It also means working closely with logistics partners to ensure they meet baseline security standards — because your resilience is only as strong as your weakest vendor link.
● Cyber-resilience focuses on continuity, not just prevention
● High-profile attacks like NotPetya exposed the fragility of tightly coupled supply chain systems
● Vendor security standards are a critical component of end-to-end resilience
Data Governance: The Foundation of a Compliant Supply Chain
Master Data Management and Supplier Data Governance
If AI is the brain of a modern supply chain, then data is the bloodstream — and bad data is like a clot waiting to cause a system failure. Master data management in supply chain ensures that product, supplier, and location data is consistent, accurate, and governed across all systems and stakeholders. Without it, you end up with duplicate vendor records, mismatched SKUs, and compliance headaches that cost real money.
Supplier data governance takes this a step further by establishing clear ownership, quality standards, and access controls around the data that flows in from external partners. For example, a pharmaceutical company managing thousands of active ingredients across global suppliers needs to know exactly where its data came from, who touched it, and whether it meets GMP compliance requirements — all of which depend on robust supplier data governance practices.
Supply chain data standardization is the enabler that makes all of this scale. Common data models — like GS1 standards for product identification or EDI standards for transaction data — ensure that when two different systems talk to each other, they actually understand what the other is saying. This is foundational for interoperability in supply chain systems.
● Master data management ensures consistency of core data across all supply chain systems
● Supplier data governance defines ownership and quality standards for external data
● Data standardization through frameworks like GS1 drives true system interoperability
Data Lineage, Auditability, and Regulatory Compliance
Knowing where your data came from and how it’s been transformed is no longer just a nice-to-have — it’s a regulatory requirement in many industries. Data lineage in supply chain systems provides a traceable path from raw data capture all the way through to reporting and decision-making, which is critical for audits, dispute resolution, and continuous improvement.
Supply chain auditability depends on having this lineage baked into the architecture from day one — not bolted on after a regulator comes knocking. Tools like IBM OpenPages and similar GRC platforms are helping enterprises build audit-ready environments that satisfy everything from FDA 21 CFR Part 11 requirements to GDPR data subject access requests.
Regulatory compliance in global supply chains is a moving target. Customs regulations, environmental reporting mandates, sanctions screening, and forced labor laws like the U.S. Uyghur Forced Labor Prevention Act all require supply chain operators to have structured, verifiable data at their fingertips. A strong supply chain compliance framework turns this from a reactive fire drill into a proactive, ongoing capability.
● Data lineage provides traceability from source to decision, supporting audit readiness
● GRC platforms help build compliance-ready environments at enterprise scale
● Global regulatory complexity requires proactive, framework-driven compliance strategies
Building the Architecture: Cloud, APIs, and Platform Design
API-Driven Integration and Cloud Supply Chain Architecture
The days of point-to-point integrations held together with brittle EDI connections are numbered. API-driven supply chain integration enables real-time, flexible data exchange between systems — whether that’s your ERP talking to a 3PL’s warehouse management system or a supplier portal feeding into your procurement platform. APIs also make it far easier to onboard new partners and adapt to changing business requirements without expensive rework.
Cloud supply chain architecture provides the scalability and elasticity needed to support these integrations at global scale. Platforms like SAP Business Network, Oracle SCM Cloud, and Blue Yonder are built on cloud-native principles that allow organizations to spin up new capabilities quickly, support distributed workforces, and integrate with an expanding partner ecosystem — all while maintaining the security guardrails that governance demands.
● API-driven integration replaces brittle, legacy EDI connections with flexible, real-time data exchange
● Cloud-native platforms enable scalable, partner-ready supply chain ecosystems
● Leading platforms like SAP Business Network and Blue Yonder support governed, cloud-first architectures
Enterprise Supply Chain Architecture and Secure Data Sharing
Designing an enterprise supply chain architecture that balances openness with security is one of the hardest problems in the field. You need your systems to be interoperable and data-rich, but you also need to ensure that sensitive commercial data — pricing, forecasts, IP — doesn’t leak to the wrong parties. Secure data sharing in supply chain often relies on techniques like data masking, tokenization, and federated data models that give partners visibility without full data exposure.
Risk governance frameworks in logistics add another critical layer. These frameworks define how risks — from geopolitical disruptions to supplier financial instability — are identified, assessed, and escalated within the organization. When integrated with the supply chain platform architecture, they enable automated risk signals to trigger workflow responses, turning governance from a manual process into a real-time operational capability.
● Secure data sharing balances partner transparency with commercial data protection
● Techniques like data masking and federated models protect sensitive supply chain information
● Risk governance frameworks, when embedded in platform architecture, enable real-time risk response