Global supply chains are under unprecedented pressure from regulatory scrutiny, cyber threats, and the complexity of multi-enterprise digital ecosystems. Organizations that invest in robust AI governance in supply chain operations and resilient supply chain architecture design are positioning themselves not just for compliance, but for competitive advantage. This guide walks through the critical pillars of building a secure, compliant, and future-ready supply chain digital infrastructure.
Why AI Governance in Supply Chain Is No Longer Optional
Artificial intelligence is rapidly transforming procurement, demand forecasting, and logistics optimization — but without proper governance, AI introduces significant risks. Supply chain IT governance frameworks must now account for algorithmic bias, data integrity, model explainability, and audit trails across complex vendor ecosystems.
According to a Gartner report, by 2026, more than 75% of organizations will adopt AI-driven supply chain tools, yet fewer than 30% will have adequate governance mechanisms in place. This governance gap creates exposure to regulatory penalties, operational disruption, and reputational risk — particularly in industries governed by GDPR, FDA 21 CFR Part 11, or DORA.
Establishing clear policies for model validation, data sourcing, and decision oversight is foundational to supply chain compliance frameworks that can withstand both regulatory audits and real-world failure scenarios.
● AI governance policies must address model explainability, bias auditing, and accountability chains.
● Supply chain IT governance should align AI deployments with existing compliance frameworks.
● Governance gaps in AI adoption represent significant regulatory and operational risk.
Zero-Trust Supply Chain Architecture: A Modern Security Imperative
Understanding Zero-Trust Principles in Logistics
Zero-trust supply chain architecture operates on a simple but powerful principle: never trust, always verify. Every user, device, and system interaction — whether inside or outside the enterprise perimeter — must be authenticated, authorized, and continuously validated before access is granted.
High-profile breaches like the SolarWinds attack demonstrated how vulnerabilities in supplier ecosystems can cascade into enterprise-wide compromises. A zero-trust model enforces micro-segmentation, least-privilege access, and continuous monitoring across all supply chain nodes, dramatically reducing the attack surface.
Supply Chain Identity and Access Management
Supply chain identity and access management (IAM) is a cornerstone of zero-trust implementation. It ensures that suppliers, logistics partners, and internal teams access only the data and systems relevant to their specific role — enforced through dynamic, policy-based controls rather than static credentials.
Modern IAM platforms integrate with enterprise directories, ERP systems, and cloud environments to deliver role-based and attribute-based access control at scale. This is especially critical in multi-enterprise supply chain networks where dozens or hundreds of external parties interact with sensitive procurement and logistics data.
● Zero-trust architecture eliminates implicit trust and enforces continuous verification across all supply chain touchpoints.
● Supply chain identity and access management must cover both internal teams and external supplier entities.
● Micro-segmentation reduces lateral movement risk in the event of a breach.
Enterprise Supply Chain Architecture and Digital Infrastructure Design
Cloud Supply Chain Architecture Fundamentals
Cloud supply chain architecture provides the scalability, flexibility, and resilience that modern global operations demand. Hybrid and multi-cloud models allow organizations to balance performance, data sovereignty, and cost while maintaining high availability across geographies.
A well-designed digital supply chain architecture separates concerns across layers — data ingestion, processing, storage, and presentation — while ensuring interoperability in supply chain systems through standardized APIs and data contracts. This layered approach supports modular upgrades without disrupting end-to-end operations.
API-Driven Supply Chain Integration
API-driven supply chain integration enables real-time data exchange between ERP platforms, warehouse management systems, transportation management systems, and supplier portals. RESTful and event-driven APIs reduce latency, eliminate manual data reconciliation, and create auditable transaction logs that support compliance reporting.
For example, a Tier-1 automotive manufacturer using API-driven integration with its Tier-2 and Tier-3 suppliers can automatically trigger procurement workflows when inventory thresholds are breached — reducing lead times by up to 40% while maintaining full data lineage in supply chain systems for regulatory purposes.
● Cloud supply chain architecture supports geographic scalability and data sovereignty requirements.
● API-driven integration eliminates data silos and creates real-time, auditable supply chain workflows.
● Digital supply chain architecture should be modular to support incremental modernization.
Supply Chain Data Governance and Master Data Management
The Role of Master Data Management in Supply Chain
Master data management supply chain practices ensure that product, supplier, location, and customer data are consistent, accurate, and trustworthy across all enterprise systems. Without a single source of truth, discrepancies in item numbers, lead times, or supplier classifications can trigger costly errors in procurement and fulfillment.
According to IBM’s MDM research, organizations with mature master data management practices achieve up to 25% faster decision-making cycles and significantly lower data remediation costs. Supply chain data standardization — encompassing naming conventions, unit-of-measure alignment, and taxonomy governance — is the prerequisite to effective MDM deployment.
Supplier Data Governance and Data Lineage
Supplier data governance establishes the policies, ownership, and quality standards that govern how supplier-provided data is ingested, validated, and used across the enterprise. This includes onboarding data quality checks, ongoing monitoring, and exception management workflows that prevent corrupted supplier data from propagating downstream.
Data lineage in supply chain systems provides a complete, traceable record of where data originated, how it was transformed, and how it influenced decisions. This capability is increasingly demanded by regulators under frameworks like the EU Supply Chain Act and the U.S. Uyghur Forced Labor Prevention Act, where organizations must prove the provenance of materials and sourcing decisions.
● Master data management supply chain practices establish a single source of truth across all enterprise platforms.
● Supplier data governance prevents low-quality external data from undermining analytics and compliance.
● Data lineage in supply chain systems is a regulatory necessity under emerging global trade legislation.
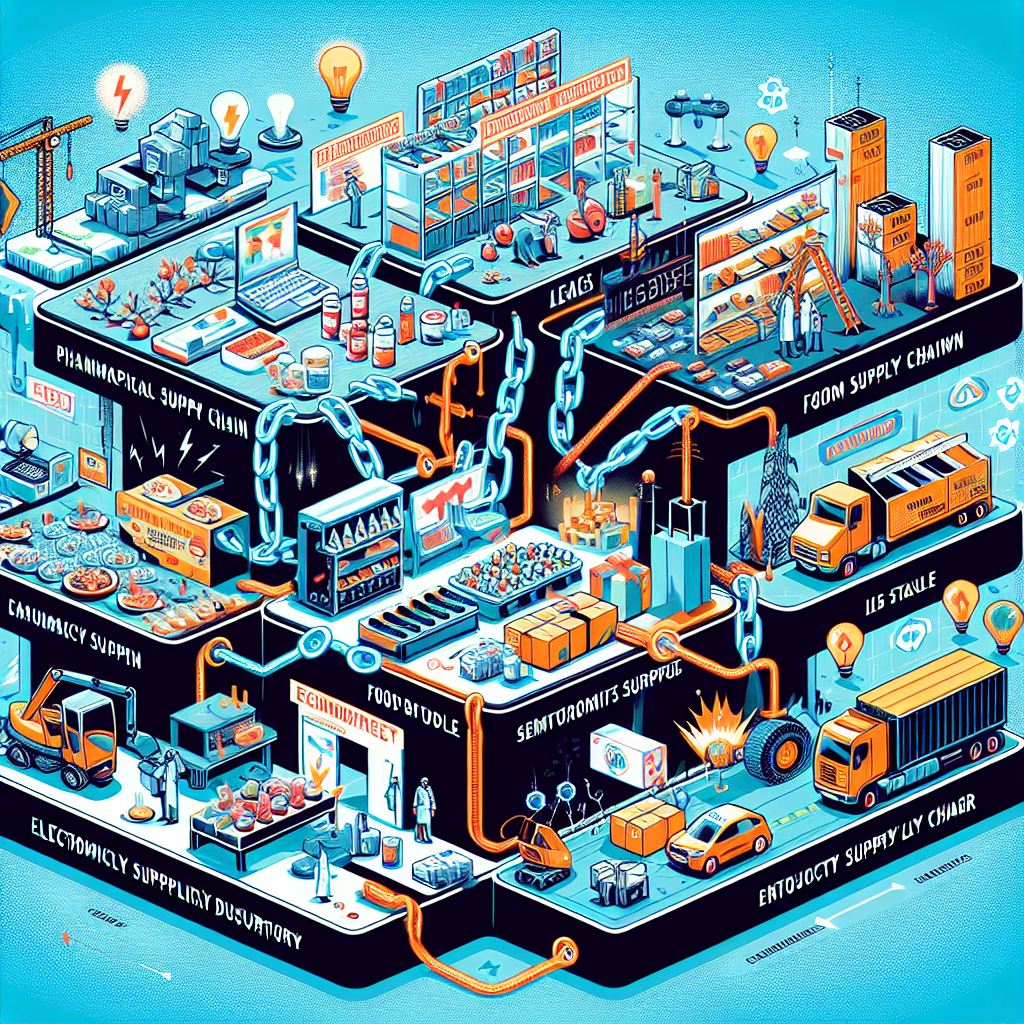
Regulatory Compliance in Global Supply Chains
Building a Supply Chain Compliance Framework
Regulatory compliance in global supply chains requires a structured, risk-tiered approach that maps legal obligations to operational controls. A robust supply chain compliance framework integrates legal, operational, and IT governance into a unified policy architecture, reducing duplication and compliance fatigue across business units.
Key regulations shaping compliance frameworks include GDPR for data privacy, ISO 28000 for supply chain security management, SOC 2 Type II for service organization controls, and CTPAT for customs and trade security. Organizations must continuously monitor regulatory changes across all operating jurisdictions and adapt their controls accordingly.
Risk Governance Frameworks in Logistics
Risk governance frameworks in logistics provide the structure to identify, assess, and mitigate risks spanning supplier insolvency, geopolitical disruption, cyberattacks, and natural disasters. They typically include risk registers, escalation protocols, business continuity plans, and key risk indicators monitored in real time.
A practical example is how many pharmaceutical supply chains implemented tiered risk governance frameworks after COVID-19 exposed single-source dependencies. By mapping critical materials to multiple qualified suppliers and embedding risk scoring into procurement systems, these organizations reduced supply disruption risk by over 35% within 18 months.
● A supply chain compliance framework must integrate legal, operational, and IT governance into a unified structure.
● Risk governance frameworks in logistics should include real-time KRI monitoring and escalation protocols.
● Regulatory compliance in global supply chains demands continuous monitoring across all operating jurisdictions.
Cyber-Resilience in Logistics and Secure Data Sharing
Designing for Cyber-Resilience in Logistics
Cyber-resilience in logistics goes beyond cybersecurity — it encompasses the ability to anticipate, withstand, recover from, and adapt to cyber incidents without significant disruption to operations. This requires integrating resilience design principles directly into supply chain platform architecture from the ground up.
Concrete resilience measures include redundant network paths, immutable audit logs, automated threat detection integrated with SIEM platforms, and tested incident response playbooks specific to supply chain scenarios. Organizations should conduct regular tabletop exercises simulating ransomware attacks on logistics systems or data poisoning attacks targeting demand forecasting models.
Secure Data Sharing in Supply Chain Networks
Secure data sharing in supply chain networks requires balancing transparency with confidentiality — particularly in multi-enterprise environments where competitors may share logistics infrastructure. Technologies such as confidential computing, tokenization, and blockchain-based data vaults are increasingly used to enable trusted data exchange without exposing raw proprietary data.
Supply chain auditability is a direct beneficiary of secure data-sharing architectures. When every data exchange is logged, signed, and time-stamped, organizations can reconstruct the full history of a transaction or decision — a capability that proves essential during regulatory investigations, product recalls, or dispute resolution processes.
● Cyber-resilience in logistics requires resilience design embedded at the architecture level, not added as an afterthought.
● Secure data sharing in supply chain networks balances transparency with confidentiality using advanced